The generic interface monitoring setup in SAP Focused Run is explained in this blog. This blog will zoom into monitoring of Idocs.
Idoc monitoring
SAP Focused Run can both report on idoc errors and delays in idoc processing. Delay in idoc processing can cause business impact and is sometimes hard to detect, since the idocs are in status 30 for outbound, or 64 for inbound, but are not processed. SAP Focused Run is one of the only tools I know who can alert on delays of idoc processing.
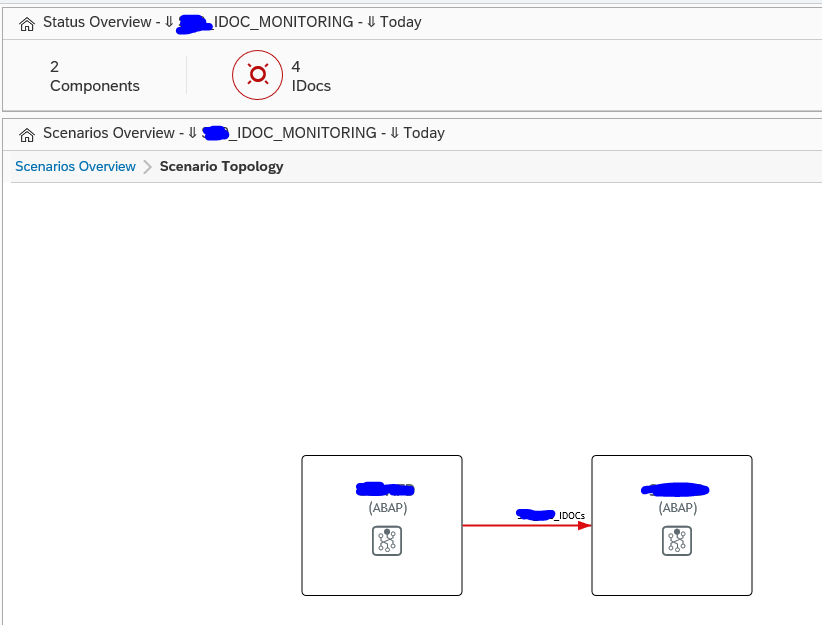
The monitoring starts with the Integration & Cloud monitoring tile:
Then select the modelled idoc scenario (modeling is explained later in this blog):
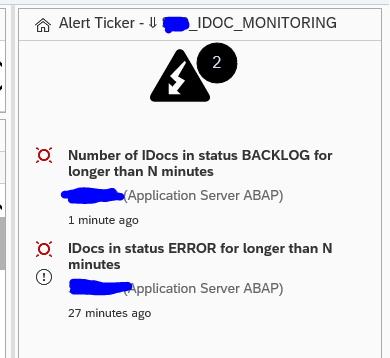
On the alert ticker you can already see there are alerts for both idocs in error, but also alerts for idocs in delay:
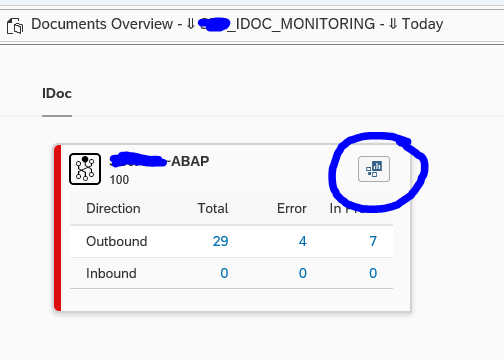
In the main overview screen click on the interface line to get the overview of idocs sent:
You can now see the amount of idocs that were sent successfully, which are still in transit and which ones are in error. Click on the number to zoom in:
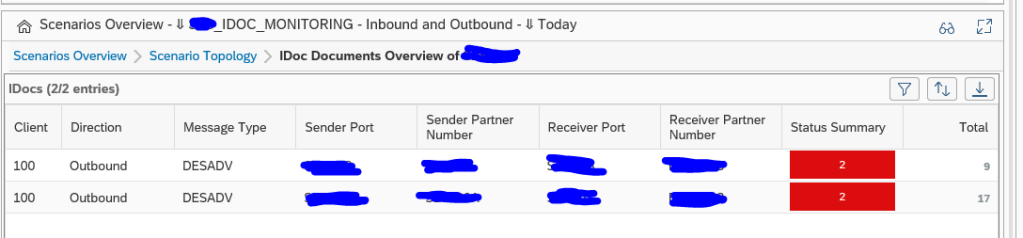
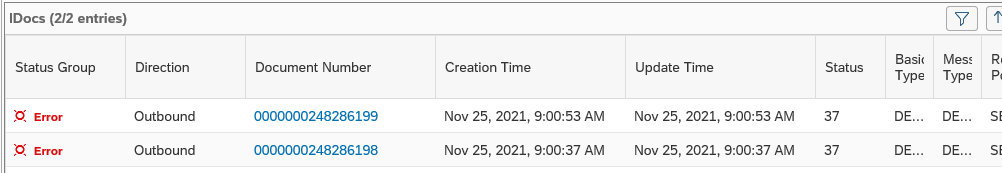
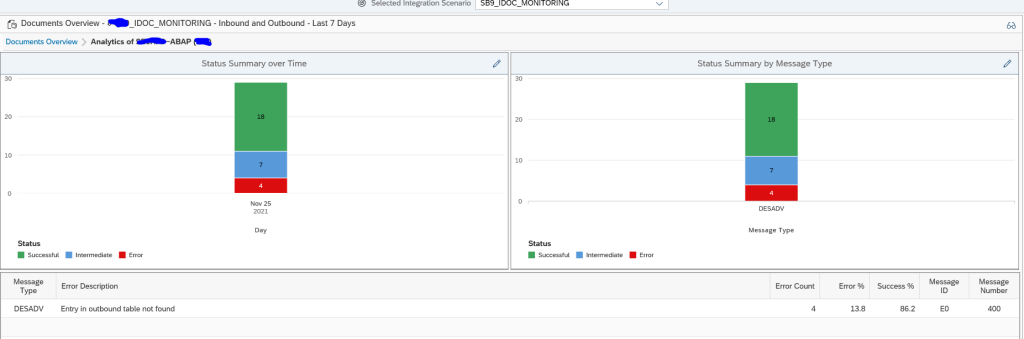
Click on the red error bar to zoom in further to the numbers:
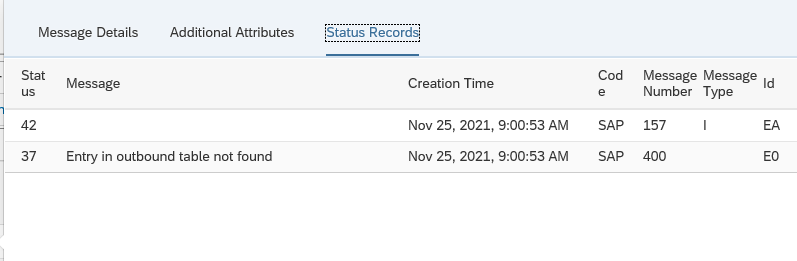
Click on the idoc number to get further details:
Unfortunately, you cannot jump from SAP Focused Run into the managed system where the idoc error occurred.
Documents monitor
A different view on the idocs can be done using the documents monitor. You can select the documents monitor tool on the left side of the screen:
Now you goto the overview:
You can click on the blue numbers to dive into the details. Or you can click the Dashboards icon top right of the card to go into the dashboard mode:
This will show you the summary over time and per message type. Clicking on the bars will again bring you to the details.
Data collection and alerting setup
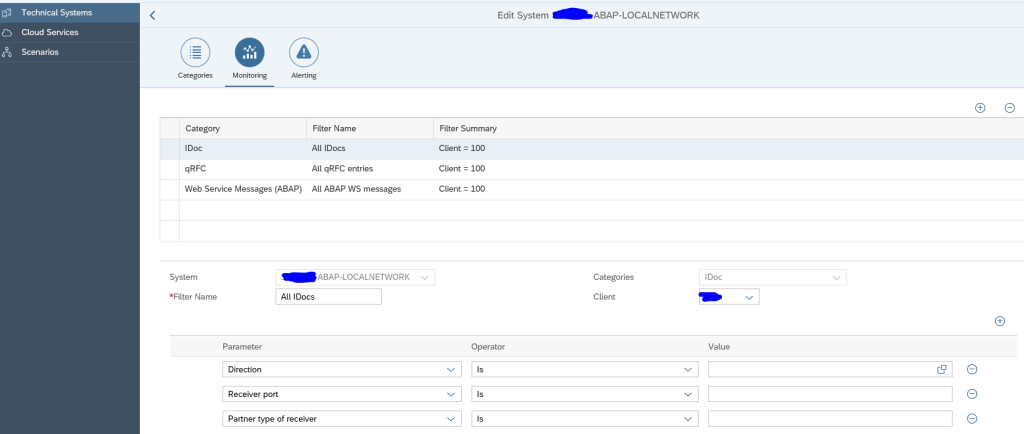
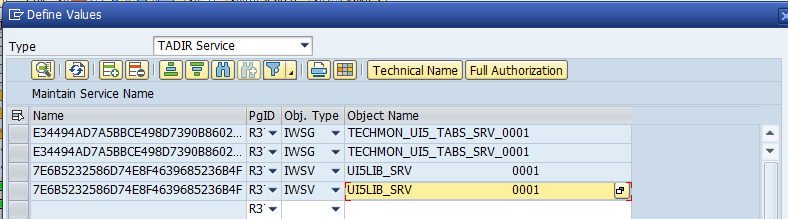
In the configuration for interface monitoring in the Technical System settings, goto the monitoring part and activate the data collection for Idoc monitoring:
In the monitoring filter, you can restrict the data collection to certain idoc types, receivers, senders, etc. Or leave all entries blank to check every idoc:
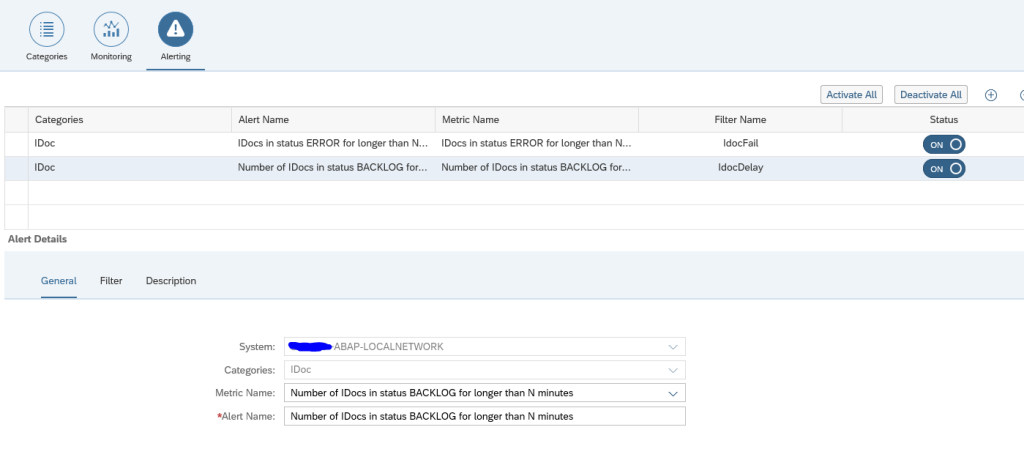
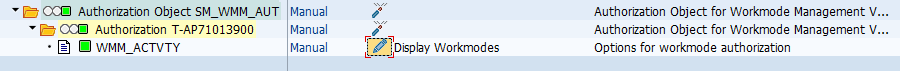
Alerting for errors
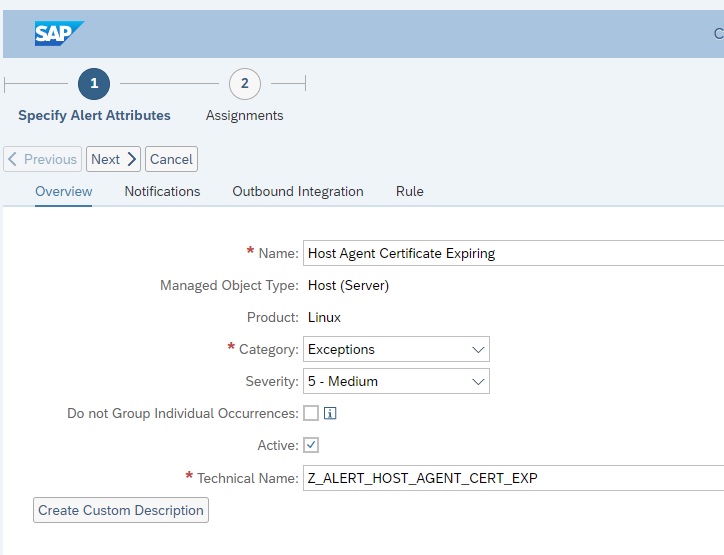
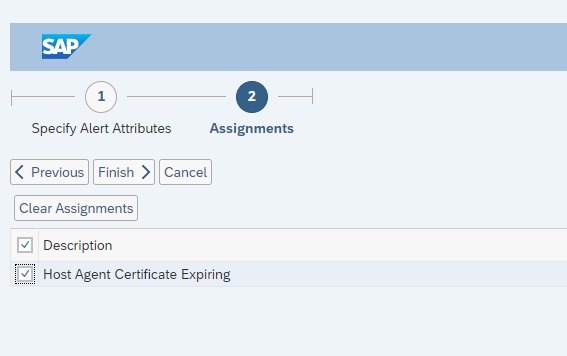
First alert we set up is the alert for errors.
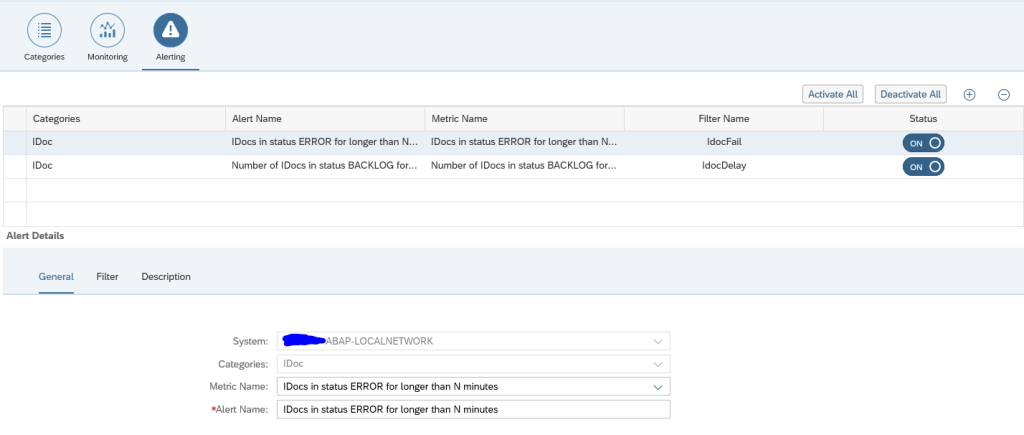
Create a new alert and select the alert for idocs in status ERROR for longer than N minutes:
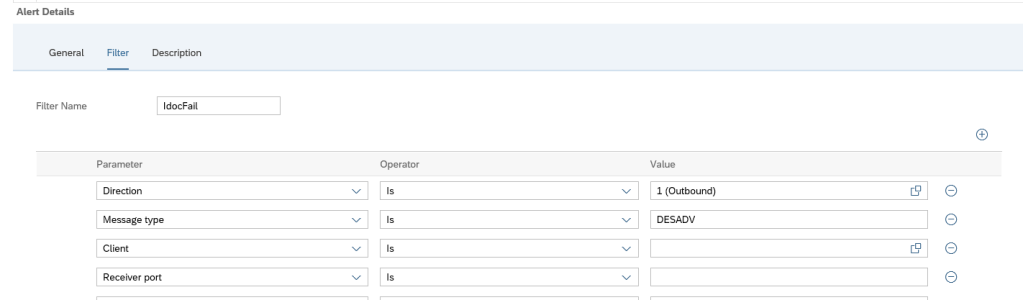
Now we add the filter. In our case we filter on outbound idocs of type DESADV:
A bit hidden at the bottom of this screen is the setting for the N for the minutes:
The time setting is depending on your technical setup of idoc reprocessing jobs (see for example this blog), and the urgency of the idocs for your business.
In the description tab add the notification variant in case you want next to the FRUN alert also mail to be sent (setup is explained in this blog):
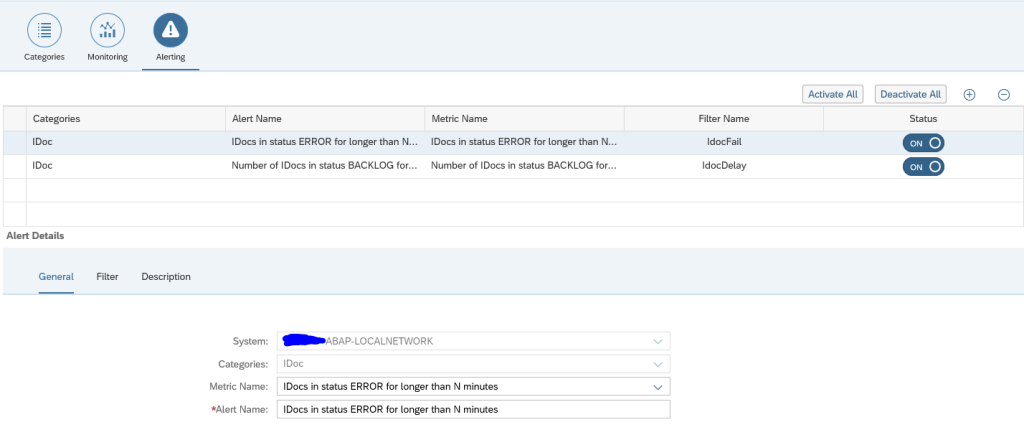
You can set up multiple alerts. This means you can have different notification groups for different message types, different directions, different receiving parties.
Save the filter and make sure it is activated.
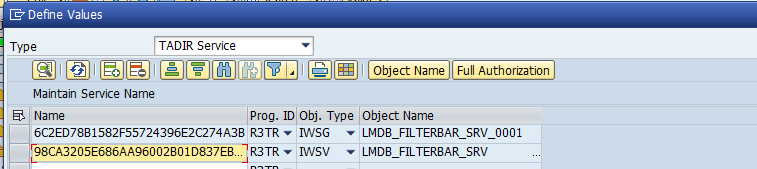
Alerting for Backlog
Next to alerting on errors, Focused Run can also alert on delay of idocs. This can be done for both inbound and outbound idocs.
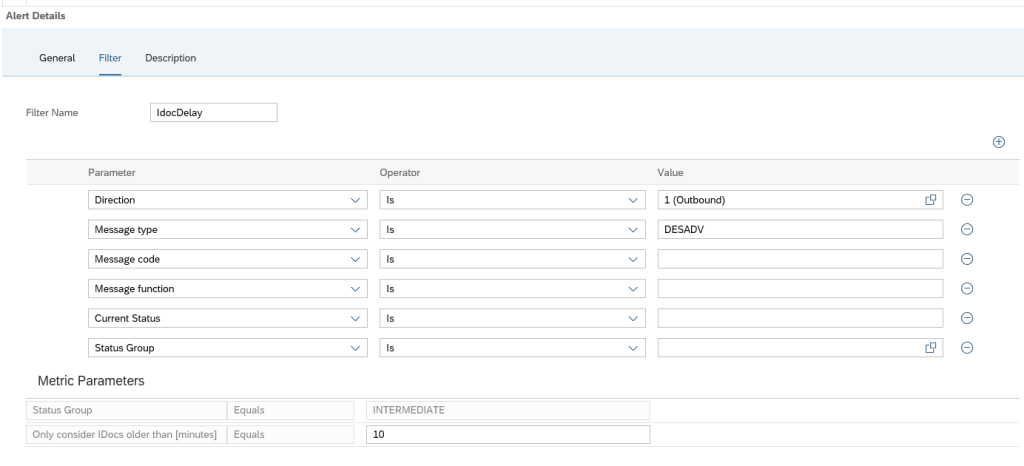
To set up an alert for backlog choose the option idocs in status BACKLOG for longer than N minutes:
In the filter tab set the idoc filter and at the bottom fill out the value for N minutes of backlog that should be alerted:
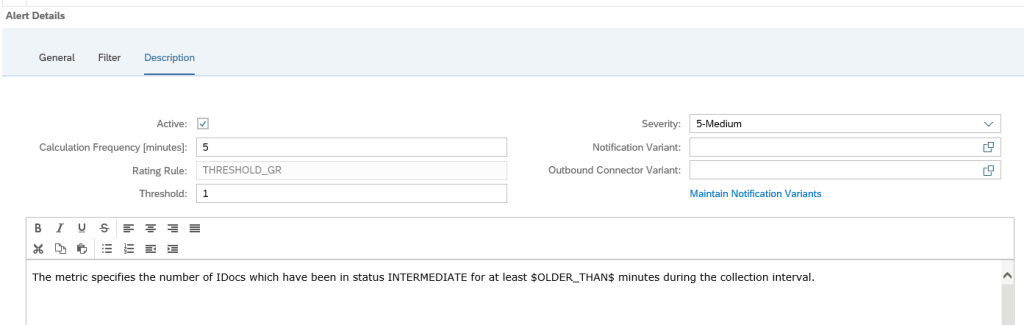
And in the final tab set the notification variant if wanted:
Save the filter and make sure it is activated.
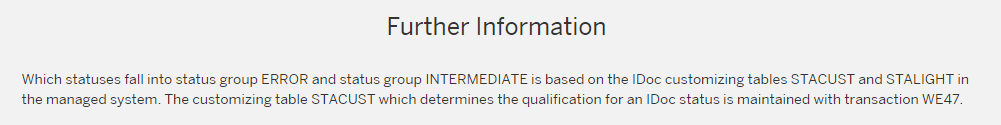
Determination of delayed and error idocs
On the SAP Focused Run expert portal on idocs, there is this definition of the determination of idocs in delay and error:
Graphical modelling
The graphical modelling of idoc monitoring is identical in principle as with RFC and qRFC. You can read the set up in these two blogs: qRFC and RFC modelling.
Data clean up
If you get too much data for idoc monitoring, apply OSS note 3241688 – Category wise table cleanup report (IDOC, PI). This note delivers program /IMA/TABLE_CLEANUP_REPORT for clean up.