With SAP Focused Run 3.0 FP 2, its now possible to monitor changes in RFCs in SAP ABAP Systems.
In SAP Focused Run 3.0 FP 2, you can activate alerting and notification for any changes to the content of a CCDB config store. Using this functionality we can activate alerting and notification on the CCDB store that contains information about RFCs.
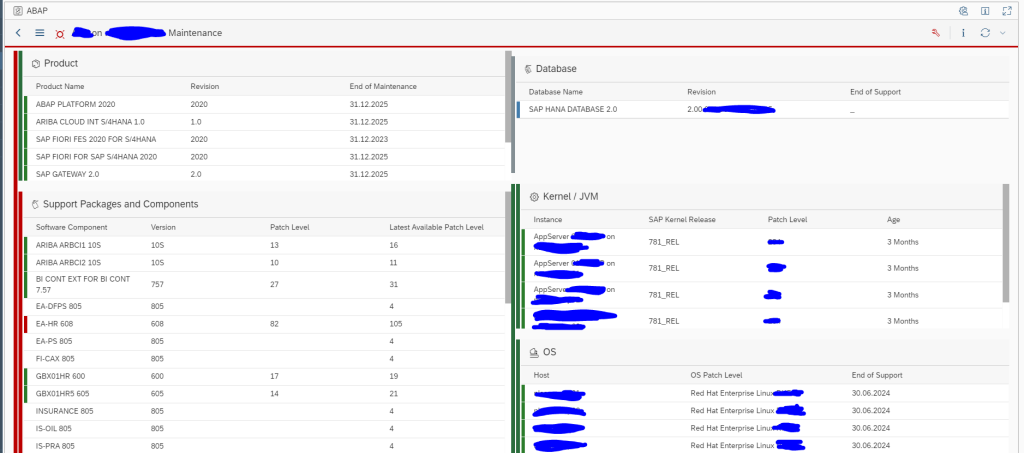
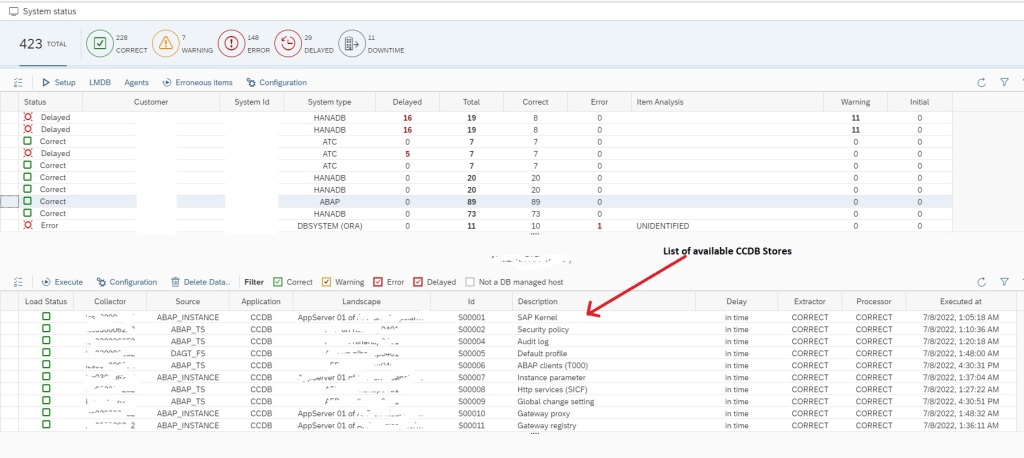
First we need to identify which CCDB store keeps the information on RFCs. For this you need to click on Configuration & Security Analytics – Administration app in the Advanced Configuration Monitoring section of SAP Focused Run Launchpad.

In the app select any of the SAP ABAP systems. Upon selecting a system you will see the list of available CCDB stores for the system.
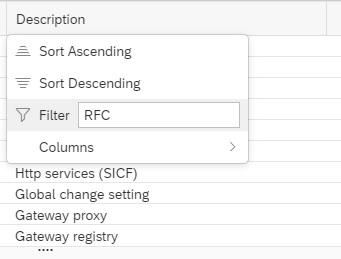
Now you can filter on Description for text “RFC” to see RFC related CCDB stores.
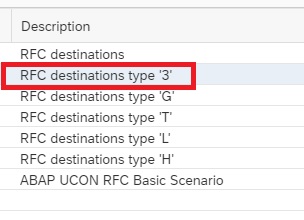
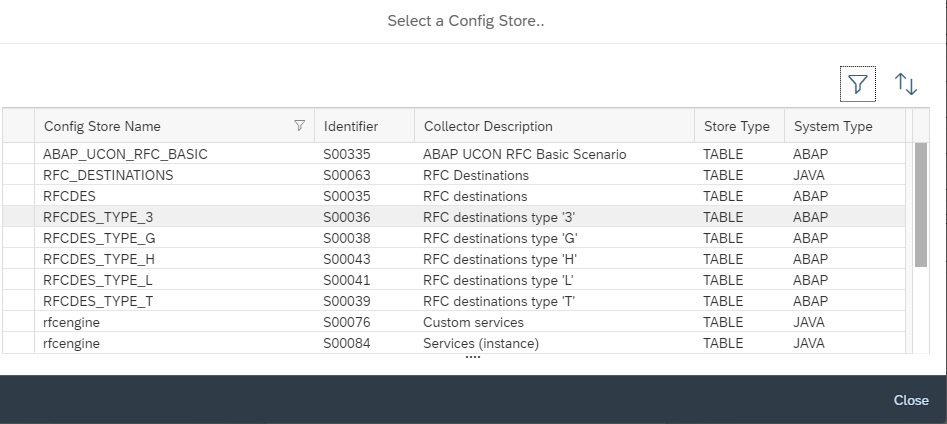
You will see the following CCDB Stores. To monitor changes to RFCs either you can use the generic CCDB store to monitor on all type of RFCs or you can use the specific RFC type CCDB store. In this example we will use the RFC destinations type ‘3’ CCDB store.
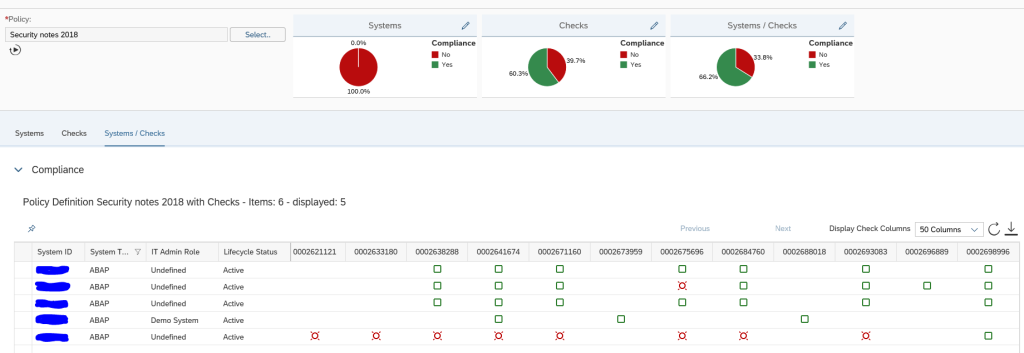
Next you need to go to the main Configuration and Security Analytics app.
In the app, in the navigation area click on Related Links.
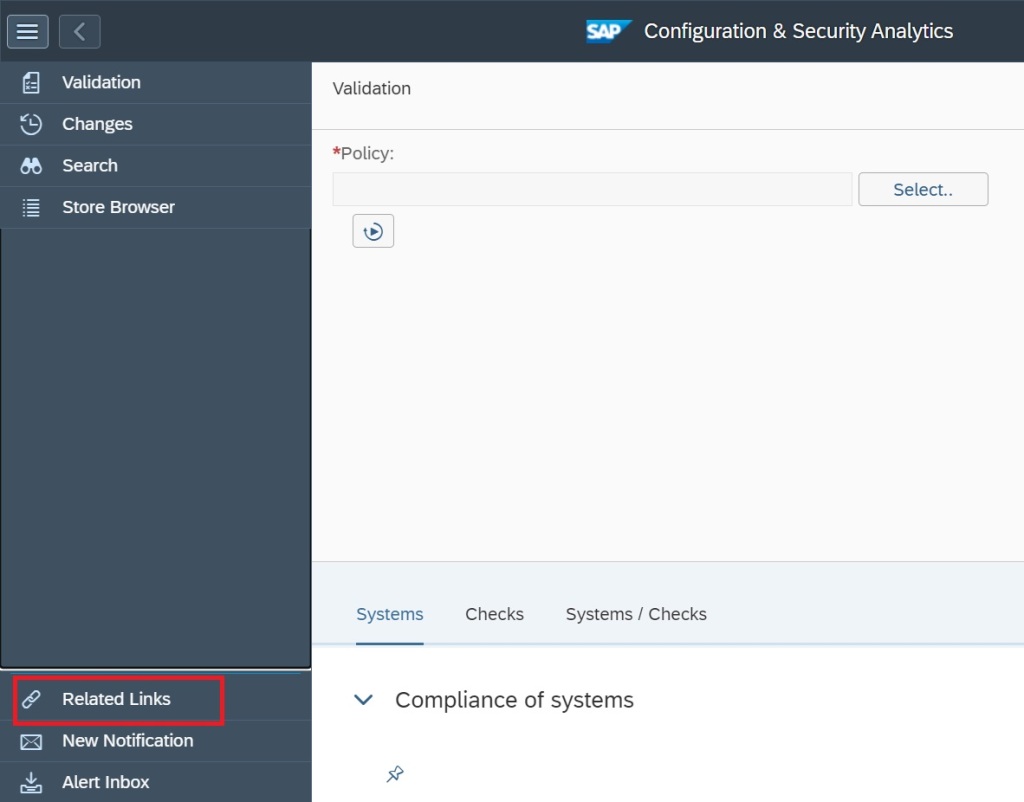
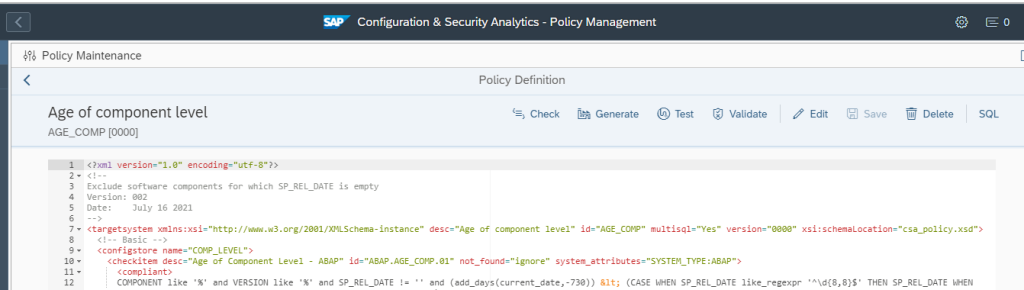
Select Configuration Validation Alert Management.
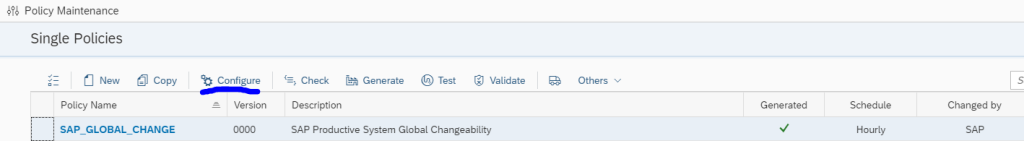
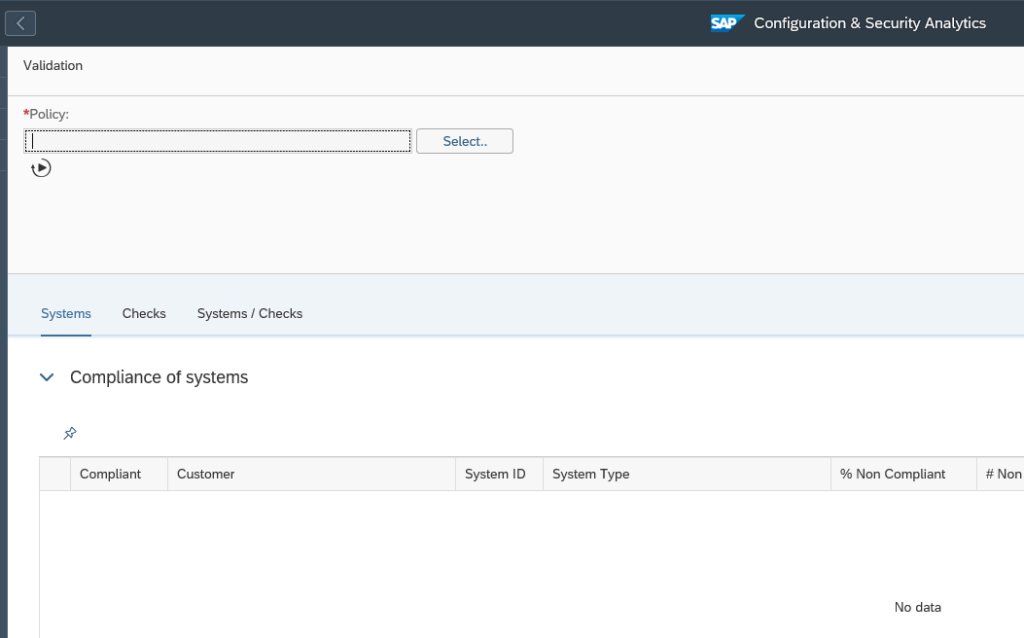
In the alert management app, click on create button.
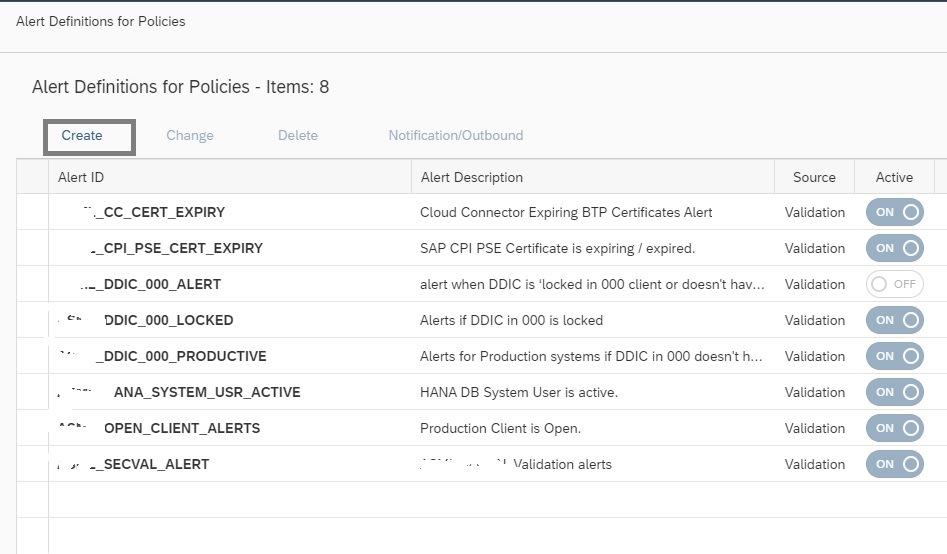
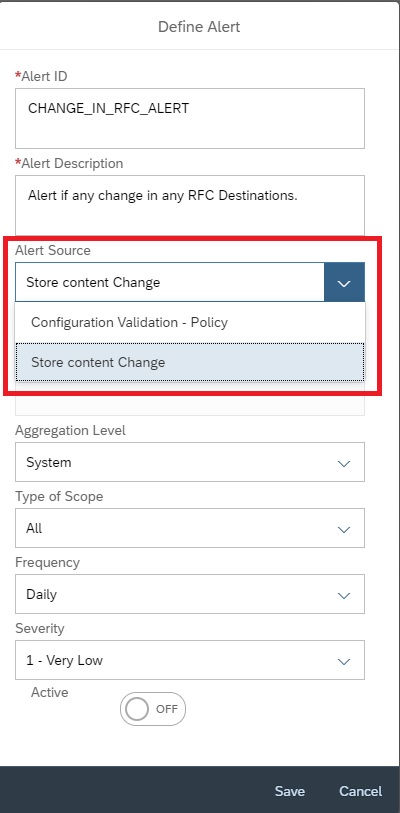
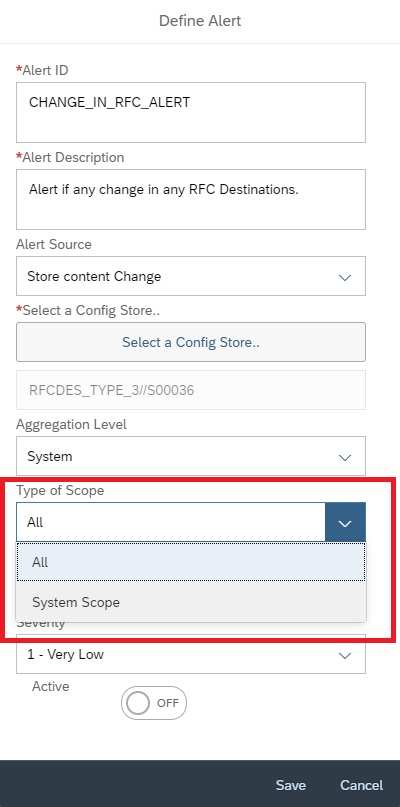
Enter Alert ID, Description and then select the Alert Source as Store content change.
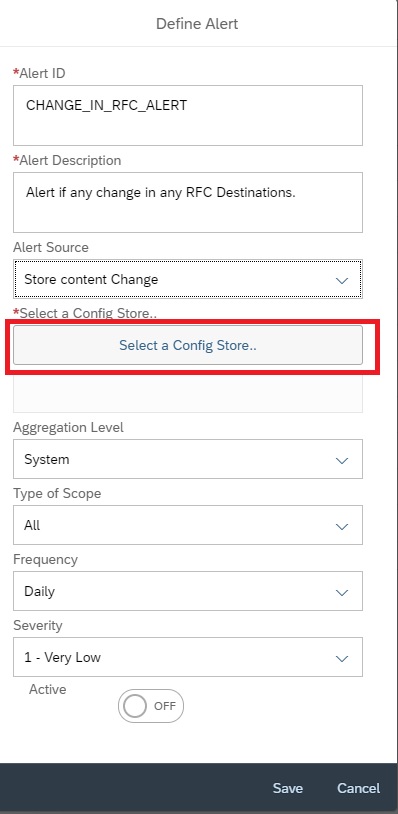
Click on Select a Config Store
In the next pop-up to select the store, filter on description “RFC”.
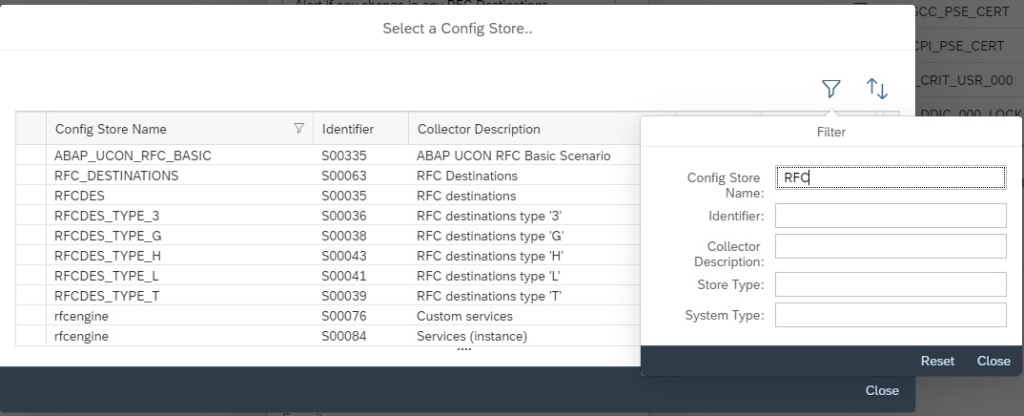
Then from the list select the specific RFC CDDB store you want to report on and then click on close.
Then back in Alert creation screen, you can select the scope as ALL or for specific system. In this example we selected a specific managed system.
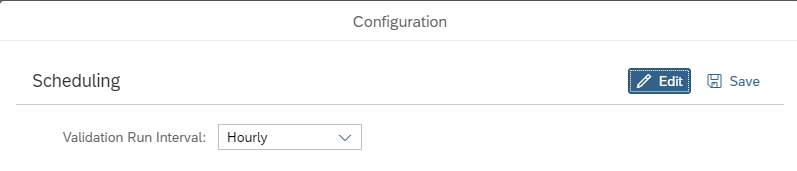
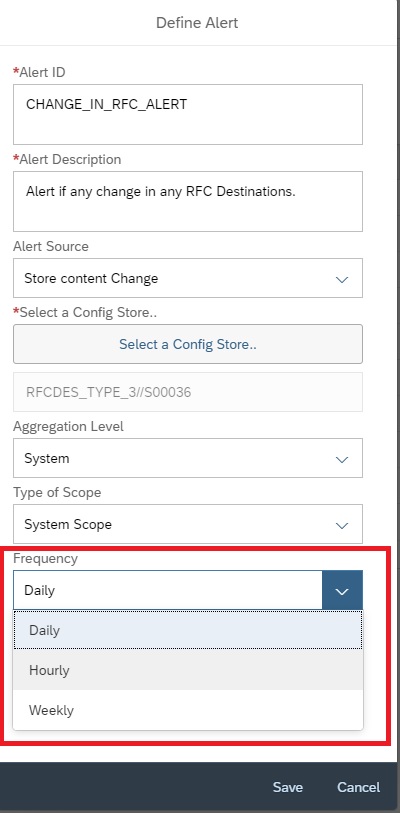
You can set the frequency between Hourly, Daily or Weekly.
Then, set the Severity and click on Active button and then save.
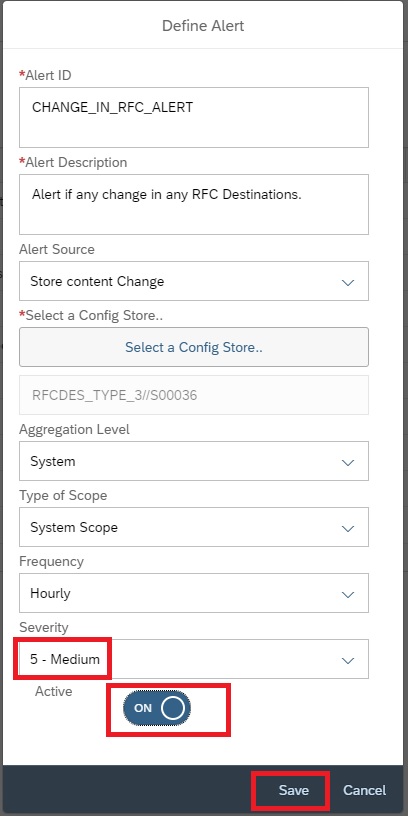
Upon activation it will start monitoring is there are any change is performed to the specific RFC store. Changes include Creation/Deletion/Update.
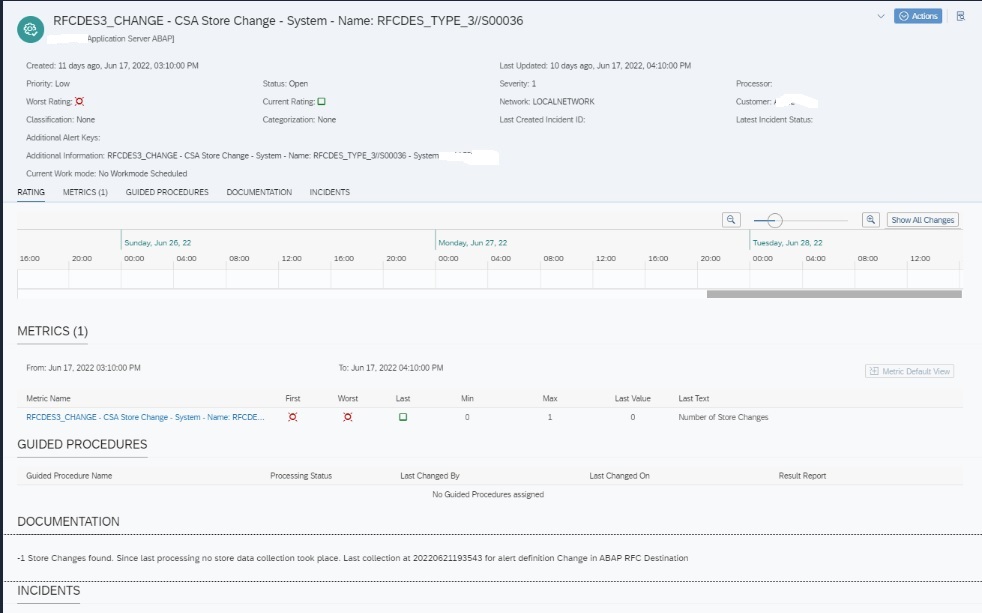
Upon any change detected an alert will be generated of the below format. This alert will be visible in the Alert Inbox.